The network is an important ingredient in any IT security plan, because cyberattacks commonly arrive from the network and attacks also use the network to propagate the damage. Network security is a huge priority for large companies, but it’s equally important for small and midsize businesses (SMBs).
Network security consists of a set of policies, practices, rules and approaches adopted to protect the integrity, confidentiality and accessibility of computer network and network-accessible resources.
SMBs can use different approaches and solutions to enforce network security:
- Network firewalls and proxies are usually used to protect the perimeter of the network and are focused on preventing remote attacks.
- Network segmentation is usually used to segregate different internal networks and minimize the attacks between segments.
- Endpoint security with antivirus, personal firewall, updated management and other solutions to increase the security of each device.
- Authentication for the company employees at a minimum, which is usually implemented with solutions like Microsoft Active Directory.
Of course, there are many other security solutions, like microsegmentation, honeypots and honeynets, system and network intrusion detection systems, and strong authentication. However, most of these solutions are too costly and too complex for most organizations without dedicated IT staff.
But SMBs can easily improve network security simply by using modern networking products.
The network and server infrastructure should be armed with the latest innovations to prevent, guard and protect against security attacks. Limiting security to firewalls and antivirus is no longer enough for any size of organization.
Network (Micro-)Segmentation
There are still SMBs with a single flat internal network, using just a perimeter firewall. This is no longer reasonable.
Most switches allow VLAN (IEEE 802.1Q) logical networks that permit some kind of network segmentation to minimize (or at least control) the internal attack surfaces.
VLANs are not the only way to achieve network segmentation. There are a lot of products and solutions to implement microsegmentation (even on a flat network), but the cost and complexity of those solutions, at this time, are out of reach for an SMB.
There are also private VLAN (PVLANs) supported on some switches that can be really useful to implement a “simple” version of micro-segmentation. For example, Aruba switches support PVLAN.
When it comes to virtual networks, VMware vSphere supports PVLAN only on Distributed Virtual Switches. That means having at least the Enterprise Plus license, which is not exactly affordable for SMBs. Note that Microsoft Hyper-V includes PVLAN support in all editions.
Having different logical segment on a physical network is only the first step. It’s like having more dedicated freeways, now you have to manage the traffic and the proper routing of it.

How do you manage the routing between logical segments? How do you manage the network security between those segments?
Using the same core switches to also manage the Layer 3 routing could be a really easy solution, but it’s not necessarily the best from the security point of view. That’s because most core switches do not provide packet filtering or packet inspection functions.
The solutions could use the same perimeter firewall to manage the different internal logical networks, but this approach could limit performance and scalability. Most SMB firewall appliances do not have enough throughput to handle internal traffic as well or may have a limited number of internal interfaces.
Another solution could be using network function virtualization (NFV) solutions, like virtual firewall (for example pfSense) or proxy.
For Wi-Fi networks, there are different considerations and solutions, but the network segmentation approach (for example for the guest wireless network) and the usage of different VLAN are still valid and normally implemented also in SMB.
Network Authentication
User (and computer) authentication is usually provided by a Microsoft Active Directory domain and is commonly used also in SMB. But what about network authentication, like Layer 2 access controls?
For Wi-Fi networks, this is something common and normally it’s implemented with WPA2-Enterprise (IEEE 802.11i). Modern access points no longer require a centralized controller, which really helps to keep the network implementation simple and affordable. Aruba’s portfolio of 802.11ax (Wi-Fi 6) and 802.11ac (Wi-Fi 5) access points address today's most challenging Wi-Fi use cases with flexible also controllerless (Instant) deployment.
But for wired networks, SMBs do not normally use specific Layer 2 network access control (NAC) solutions. And it’s a pity because most switches support Layer 2 network authentication based on IEEE 802.1X standards. And, of course, common endpoints like Windows, Linux or MacOS based also support those standards.
Unfortunately, you need also infrastructure (basically an authentication server that supports the Radius protocol), but you can implement it also with Windows Server with the NPS feature. It’s probably still too complicated for an SMB but it can really increase the network security. There are also specific products to simplify a NAC implementation (like Aruba ClearPass), but in most cases they are focused for enterprise and not for SMB.
Network Confidentiality
For Wi-Fi networks, all the communications are encrypted by default and cipher suites are evolved to make this encryption secure.
But for wired networks, the switches do not provide any secure channels (because of the nature of Ethernet) and it’s up to the application (or session) layer provide better secured communication.
Application protocols have been replaced gradually with an encrypted version of the same protocols (like HTTPS instead of HTTP) and, of course, client and server have changed to support those protocols.
Also, network protocols, which were initially designed for internal communication, have been improved to have secure channels, as has happened with SMB or RDP protocols in Windows systems.
Providing an end-to-end secure channel is becoming the standard and can really increase the overall network security.
Network Visibility
For the SMB, providing network analytics in a simple and cost-effective way is probably one of the most difficult aspects.
There are several free tools that can provide aggregated values, like network traffic. But these tools become difficult when you want to search or analyze or if you need a proactive way to check your network traffic and find network security issues.
From this perspective, SaaS cloud offerings could be a better solution for SMBs. You can just rent a service without buying the complex infrastructure that you need to run it.
Also, machine learning and artificial intelligence are used in those tools to provide more valuable information or permit deep automatically analysis.
The Big Picture
Network security is a complex argument and requires a set of different solutions with good integration and compatibility. Standards may help, but there aren’t enough standards for the different security aspects out there.
For this reason, different vendors build their “packaged solutions.”
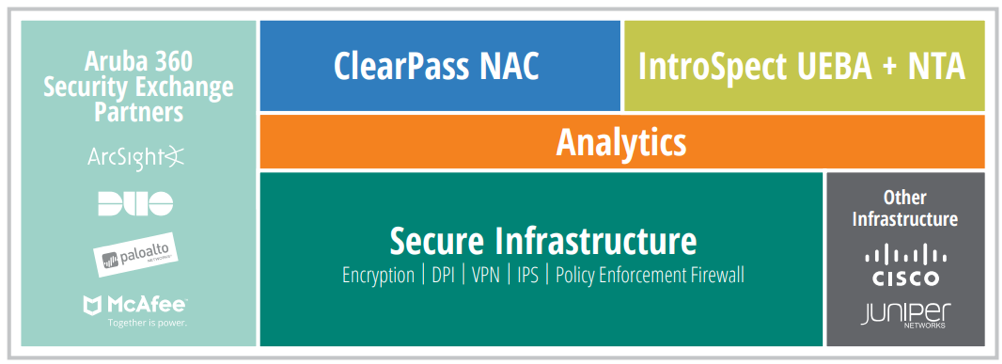
For example, the Aruba 360 Secure Fabric is an enterprise security framework that gives security and IT teams an integrated way to gain visibility, control and advanced threat defense.
Of course, those solutions are mostly designed for enterprise, but the history tech that several solutions born for the enterprise case have been adapter also for SMB.
Learn More
Get an overview of HPE networking security solutions.
Learn more about the family of Aruba switches.




