A slide from Gartner analysts Avivah Litan and Tony Bussa's presentation at the annual Gartner Security and Risk Management Summit struck me as so relevant to how security ought to evolve. In her presentation on analytics, Avivah highlighted a framework to think about analytics. The application of analytics for cybersecurity and insider use cases can be viewed as a spectrum comprising:
- Descriptive analytics: Analytics to explain anomalous events that are happening. For example, malware communicating on the endpoint.
- Diagnostic analytics: Analytics that can help identify why something happened. For example, user Joe clicked on an email attachment or often long after the incident may have happened.
- Predictive analytics: Analytics that can help predict stuff before damage is done. For example, user Joe is starting to behave very strangely and likely to be putting your data at risk.
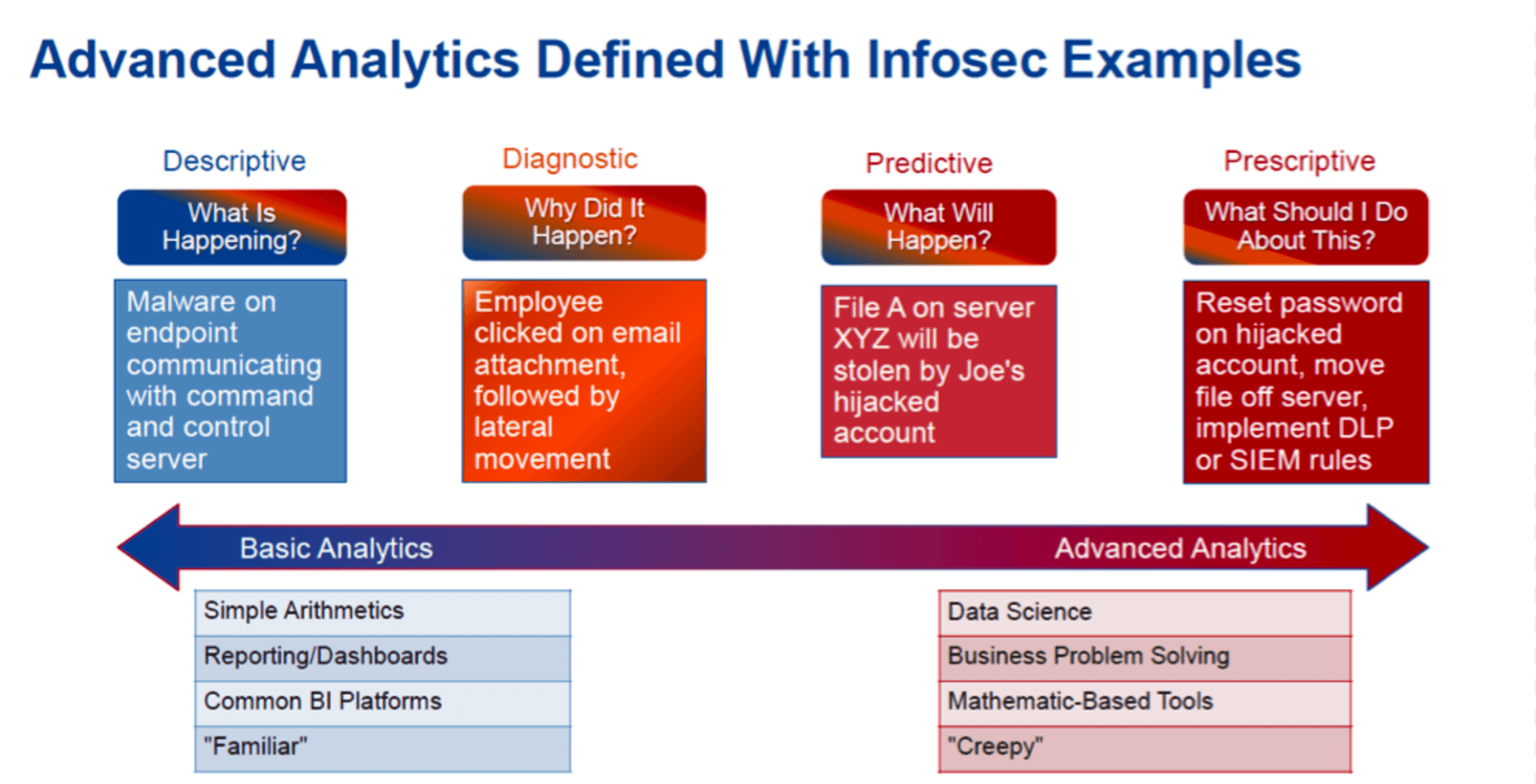
Figure 1: Gartner Presentation, "The Fast-Evolving State of Security Analytics 2016", Avivah Litan and Toby Bussa, Gartner Security and Risk Management Summit, 13-16 Jun 2016
The part about "predictive analytics" caught my attention, given the lack of focus thus far by security solutions on more proactively helping customers identify security incidents in their environment before the damage is done. Traditional systems have focused on either detecting the infection (IDS or specialized threat analysis and protection solutions) or exfiltration (DLP products) stages.
There is increasing evidence that just focusing on the infection stage is insufficient for many of the cyber threats of today. The issue with looking at detecting incidents that are in the exfiltration stage is that it may be too late for these detections at this stage to stop the threat before the damage is done. After all, what good is it if the security analyst just found out that a user has uploaded a bunch of sensitive documents to their personal Dropbox account? Would he/she be in a better position if there would have been advance warnings to the possibility of this happening?
Most modern attacks are typically multi-stage, involving many of the activities along with numerous dimensions and often involve many stages prior to the eventual exfiltration phase as shown in Figure 2 below.
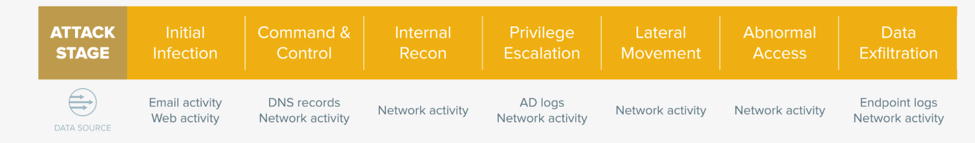
Figure 2: Diagram showing the stages of infection and data loss as well as the data sources needed for analytics to accurately detect the various stages
This is why predictive analytics offers much promise to detect many of these attacks and security incidents prior to the exfiltration phase and stop them before the damage is done. What if there were ways to rapidly identify situations in a proactive manner? For example:
- Michele is likely to be exfiltrating data in the near future because her account appears to be compromised.
- Joe is likely to be walking away with your firm's sensitive information because he accessed sensitive information in a very unusual manner.
- Bob is at risk of leaving the company because the sum total of his behavior inside the network looks very different compared to how he normally behaves. For example, he is more active on job sites or appears to be checked out.
This could potentially help analysts detect, investigate and stop these incidents before sensitive data leaves your network and the damage is done. The predictive analytics detection scenarios could cover the early detection of compromised users who are under the influence of an attacker as well as insiders who may be acting in a negligent or malicious manner.
Given the likelihood of several stages during most attacks/security incidents between the infection and exfiltration stages, detecting as many of these stages as possible will best position your organization to thwart these threats. Raising an alert based on detection of only one activity or one stage will generate excessive false positives. What's needed to ensure that only high fidelity incidents are escalated to an analyst for resolution require the ability to thread a needle through anomalous behavior across multiple stages and paint a comprehensive, macro picture into what may be truly happening to the user or host. This would give a tremendous leg up to security analysts to stop attacks before the damage is done.
Interested in learning more? Learn how Aruba IntroSpect predictive analytics uses behavioral techniques to help detect and stop advanced threats before the damage is done.




