
This blog is part of a continuing series on Aruba’s Dynamic Segmentation solution. Check back for continued insights.
What do you think of when you hear the term “micro-segmentation”? For me, the first thing that comes to mind is the data center, where micro-segmentation is used to securely separate cloud and data center workloads based on policies. But segmentation doesn’t just end at the data center—increasingly we’re seeing practical applications at the edge as well.
Driven by the growing number of Wi-Fi users, the rising IT investment in public cloud infrastructure and the ballooning number of mobile and IoT devices in the workplace, we’re seeing a fundamental shift in the role of campus and branch networks that is wreaking havoc to traditional edge architecture—but it’s also offering IT a chance to combine the best networking technologies from the campus and data center to manage this complexity.
There are three key changes I see at the edge:
- Traffic is shifting from east-west (client to client) to north-south (client to the Internet).
- Applications are now being hosted in public cloud infrastructure (IaaS and SaaS).
- A growing number of business decisions are now being made at the edge
The first two are fairly simple, but the third is more difficult to manage. The business is converging on the network even as it’s rapidly expanding technology use cases beyond the realms of IT—IoT itself generates a massive amount of data.
The underlying network fabric has become a veritable melting pot of activity where every new device or every new application can mean countless configuration changes that impact SSIDs, ACLs, VLANs and subnets at every hop in the network – as well as looming threats to network security and visibility.
So let’s take a look at how Aruba is addressing these challenges.
What is Dynamic Segmentation?
Aruba’s Dynamic Segmentation is a solution that simplifies and secures the network by unifying policy enforcement across the wired and wireless access layer. With a unique user firewall, Layer 7 application visibility, and automated profiling, Aruba’s unified policy enforcement engine can apply rich, role-based access control to automatically shape traffic behavior.
Since policies define access and segmentation, there’s no need to configure VLANs, ACLs, subnets or port-based controls anymore. This eliminates complex network segmentation, sprawling VLANs and costly administrative functions.
The graphic below shows a left-to-right flow for how traffic can be segmented across the network based on the applications being used by users and devices. With Dynamic Segmentation, traffic flows simply adapt to the assigned user and device roles.
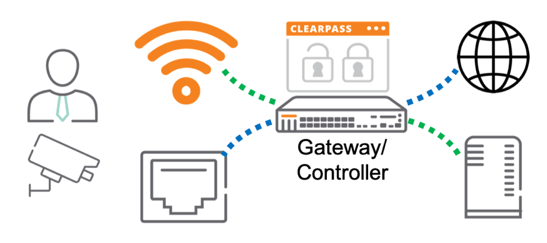
As you can see, ClearPass and the Mobility Controller are instrumental in Dynamic Segmentation. All wired and wireless traffic is encapsulated in GRE tunnels back to a Mobility Controller for inspection by the built-in Policy Enforcement Firewall (PEF). This is where the user firewall and Layer 7 application visibility reside. ClearPass is used to create contextual policies based on identities, device type and location for different groups of users or devices. ClearPass provides centralized policy definitions and integrated device profiling capabilities.
Three Reasons to Use Dynamic Segmentation
The need for policy-centric networking is growing. Organizations are increasingly converging multiple systems onto the same infrastructure, and they need to segment that traffic more efficiently and securely. They may need to protect sensitive applications and ensure data privacy in a more highly controlled way. They may be rolling out IoT systems, such as video surveillance, building access control or smart lighting, and want to ensure that any IoT device vulnerabilities don’t spread across the organization.
At the same time, IT needs more visibility and control of devices that are on their network. The reality is that most IT managers simply aren’t aware of all of the connected devices—and with the embrace of IoT and smart workplaces, this problem is only going to get worse. IT needs visibility into what devices are on their network as well as a way to control network access and the quality of experience for those devices in real-time.
Dynamic Segmentation can:
- Automate policy to reduce the IT workload — Dynamic Segmentation reduces the burden of manual configuration. It saves time and energy that IT would otherwise spend configuring managing access policies for mobile, IoT and other devices—and any ongoing moves add and changes (MAC). Automated policy also minimizes the errors that creep in when configurations are done individually. Strong, consistent controls across both wired and wireless access are imperative to maintaining integrity and preventing breaches.
- Segment policy to enhance security – With Dynamic Segmentation, users and devices are granted access to the appropriate network route based on their role, location, time of day and other factors. Dynamic Segmentation is ideal for IoT. IoT deployments like automated lighting, security cameras and secure-access doors bring many benefits, but they also create security risks if these devices are on the same network route as sensitive or critical business data. IoT devices are notoriously insecure and are often located in unsecured public areas. But now, security cameras can be dynamically assigned roles with rights that restrict their traffic to a specified server, and nowhere else.
- Centralize policy to ensure enterprise-wide consistency – Admins can define rules that leverage user, device, application and location data—all from one place. With centralized policies, there are no variations based on the location or the style of the network administrator. Policy changes don’t need to be made multiple times for each individual network element. Policies are consistent and up-to-date everywhere in the enterprise. And policy is enforced within a broader context.
Dynamic Segmentation, leveraging ClearPass and Aruba wired and wireless networks, can simplify network operations and improve visibility and control over all kinds of devices, including IoT.
My next blog will dive into the key building blocks for Dynamic Segmentation as well as two ways you can take it to the next level.
Related Content
See a demo from last year’s Tech Keynote and read the Dynamic Segmentation solution brief.
Learn more about how Dynamic Segmentation can support IoT in this blog by my colleague Sue Gillespie.




