 This blog is the third in a series that explores how organizations can use Aruba’s Dynamic Segmentation. In the first blog, I explored how Dynamic Segmentation can simplify and secure and secure networks. In the second blog, I focus on the growing challenges of enforcing application policies. In this blog, I focus on how dynamic segmentation can improve device visibility, which is also getting more challenging.
This blog is the third in a series that explores how organizations can use Aruba’s Dynamic Segmentation. In the first blog, I explored how Dynamic Segmentation can simplify and secure and secure networks. In the second blog, I focus on the growing challenges of enforcing application policies. In this blog, I focus on how dynamic segmentation can improve device visibility, which is also getting more challenging.
Competition for talent is fierce in a tight labor market, and Acme Global Marketing has been modernizing its offices to appeal to tech-savvy Millennial and Gen Z workers. Smart sit/stand desks let people adjust their desk height and track their activity goals. Workers can control the light and temperature to their liking, while saving energy. A new visitor management system frees up the receptionist, and employees use a mobile app to find an open meeting room. Security cameras have improved physical safety, and employees open doors with their phones.
Acme employees love the additions, but the new digital workplace is creating a problem for Priya, the IT manager. Suddenly there are hundreds of unknown devices connected to the network. Sure, she knows that the mysterious devices are really sensors, smart machines and other IoT devices, but without any real visibility, she’s worried that a rogue device or cyberattacker is hiding in the network.
Workplace IoT Meets Traditional Devices
Whether or not your company is ready to install smart lighting and Kombucha on tap, there’s no question that every office network has a lot more types of devices connected than ever.
The harsh reality is that IT doesn’t always know what, where and when IoT devices are connected to the network – and that poses a big risk. Many smart devices are new to the market, and are often made by companies that don’t have deep expertise in networking or cybersecurity. It can be very difficult for traditional IT asset management systems to identify these new device types in any helpful detail. And that leaves potential gaps that criminals could take advantage of.
Know What’s On Your Network
Fortunately, Acme Global Marketing has an Aruba network.
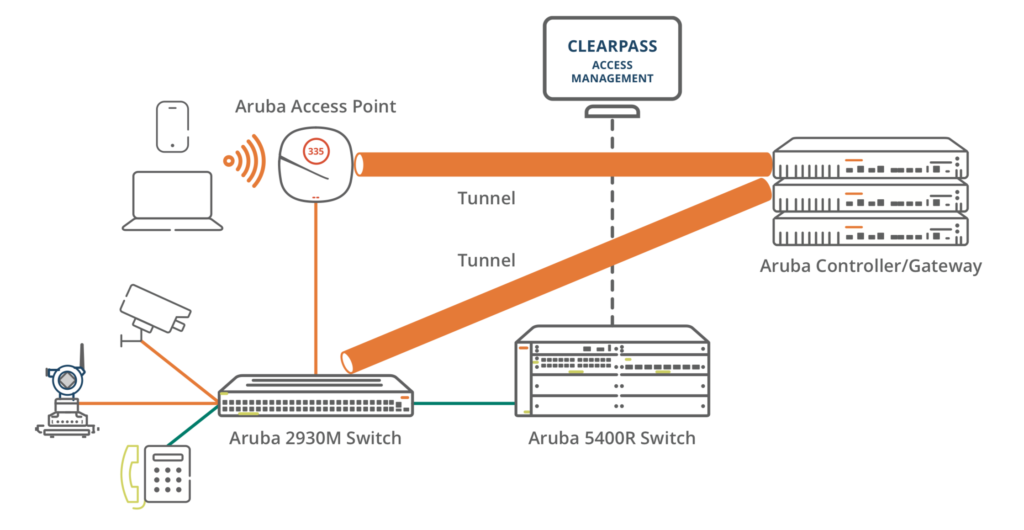
Priya used the Aruba Policy Enforcement Firewall to provide automated Dynamic Segmentation functionality for Acme’s wired and wireless network. With the Aruba Dynamic Segmentation solution, smart office and other IoT devices automatically have their own virtual network segments, and IoT device traffic doesn’t mix with corporate applications.
 Aruba ClearPass Device Insight provides full visibility into all connected devices, whether traditional or IoT. Not just that, but it leverages machine learning and crowd-sourced data so that Priya doesn’t need to fill in device profiles from scratch. Priya can see contextual information such as device type, vendor, hardware version and behavior such as applications and resources accessed. She created roles for different users and device types, so the appropriate network-assigned role, access privileges and policy always follow the user and device.
Aruba ClearPass Device Insight provides full visibility into all connected devices, whether traditional or IoT. Not just that, but it leverages machine learning and crowd-sourced data so that Priya doesn’t need to fill in device profiles from scratch. Priya can see contextual information such as device type, vendor, hardware version and behavior such as applications and resources accessed. She created roles for different users and device types, so the appropriate network-assigned role, access privileges and policy always follow the user and device.
So now, for example, smart lighting system sensors are automatically identified, and only allowed to access the cloud software from the lighting vendor. Unknown devices can be given limited access or kept off the network entirely.
Priya has far greater visibility into the devices on the network, and there are far fewer devices classified as “unknown” on the network. The appropriate policies can be applied, and the risk of rogue devices is mitigated. Employees of Acme Global Market can personalize their workspaces without worrying about cybersecurity.




