In a previous blog, I explored why 802.11ax means more IoT. 802.11ax, now known as Wi-Fi 6, makes the WLAN even more IoT-friendly given the support for dense concentrations of clients in environments like buildings that may have smart lighting, environmental controls and meeting room technology.
 Wi-Fi 6 introduces some terrific new security features, but the IoT risk is rising fast.
Wi-Fi 6 introduces some terrific new security features, but the IoT risk is rising fast.
The security surrounding IoT devices has lagged behind hackers’ ability to penetrate these devices. Criminals can remotely control smart devices, creating traffic jams on highways, disrupting the power grid or interrupting industrial robots. A compromised IoT device can serve as a springboard for an attacker to spread through the network and steal or destroy sensitive information.
Examining the IoT Security Gap
To better understand the perceived challenges of securing IoT and how IT security professionals expect to deal with those challenges, we at Aruba partnered with the Ponemon Institute who surveyed 3,866 IT and IT security practitioners in Asia-Pacific, EMEA and North America.
Here’s some of what we found out:
- <25% of Ponemon survey respondents believe IoT devices are secure
- 66% say they have little or no ability to secure IoT devices
- 60% believe even simple “things” pose a threat
These stats aren’t surprising. I’ve always found IT security professionals to realists.
IoT devices often lack the compute or battery power to be secured by traditional endpoint security methods. They don’t log their activities. They can turn on and off, disappearing from the network, until they’re needed.
That elevates the role of the network itself to secure IoT devices. In today’s threat landscape, the only way to determine if a device has been compromised is to monitor and analyze network traffic. More on that in a minute.
The Ponemon study also asked about IT professionals’ preferred approaches to secure IoT devices, and the respondents identified multiple approaches:
- continuous monitoring of network traffic
- network access control
- closed-loop detection and response
- peer group/anomaly detection
The business responsibility for the IoT applications and devices itself may often lie with manufacturing, operations or another business group. Not the IT department. In fact, the study shows that responsibility for IoT security has not been centralized. The CIO, CISO and CTO and the line of business were all named as responsible for IoT security. Thirty-three percent said the CIO, but interestingly none of the other functional roles registered above 20% and “no function” came in third at 15%.
Aruba Helps Close the IoT Security Gap
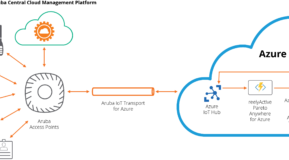
Aruba provides 360-degrees of active protection to help organizations close the IoT security gap and move ahead with innovative, transformative projects that bridge the physical and digital worlds.
At Aruba, we believe that the combination of network access control and user and entity behavior analytics is powerful. Together, Aruba ClearPass, and Aruba IntroSpect Network Traffic Analysis (NTA), deliver a security solution that’s particularly tuned to mitigate the risks of IoT.
ClearPass provides intelligent network access control for both wired and wireless networks. It can discover and fingerprint IoT, mobile and all other devices and enforce the appropriate policies. IntroSpect integrates advanced AI-based machine learning, pinpoint visualizations and instant forensic insight. Attacks involving malicious, compromised or negligent users, systems and devices are found and remediated before they can damage the operations and reputation of an organization.
Learn More
Blog: 802.11ax means more IoT. Now, how do I secure it?
Blog: After All the Hard Work, Why Does the Security Gap Still Exist?