I’m fired up about Security Field Day on Fri., Dec. 14. Before the event, I had an opportunity to catch up with Ethan Banks, cofounder of PacketPushers Interactive, to find out what he’s been up to recently, his views on the some of the big challenges in cybersecurity and who inspires him in this field. Follow Ethan on Twitter at @ECBanks and don’t miss the great content at PacketPushers.
Jamie Easley: What’s been going on at PacketPushers since we last connected for Network Field Day?
Ethan Banks: We launched the Virtual Design Clinic, which is aimed at folks without a travel budget. It’s very interactive. We have ask-me-anything panels, which gives people in the audience a chance to ask questions and have a discussion. The AMA panels are run by people who are up to their necks in data centers and have experience building automation and orchestration. We’re focusing on topics that people are struggling with or trying to figure out how to implement. We want to inspire folks to get started.
We also launched a membership site called Ignition. People who want to support the podcast network directly can get access to exclusive content. We’ll also have analytic whitepapers, technical how-tos and exclusive podcasts.
 JE: In the previous interview, you said you love to be outdoors when you’re not knee-deep in technology. As winter approaches, what do you do outside?
JE: In the previous interview, you said you love to be outdoors when you’re not knee-deep in technology. As winter approaches, what do you do outside?
EB: I’m getting ready to do a series of winter peak bagging. You go after some summit, and get it. Winter in New Hampshire is snowy, windy and cold, so I’m beefing up my winter equipment. As soon as it’s officially winter—December 21—I’m going to be going out aggressively on the weekends, and weather permitting, heading into the wilderness.
JE: Let’s talk a bit about security. What’s the biggest security risk that you think people consistently overlook or don’t know about?
EB: It’s social engineering. A lot of breaches happen because bad actors take advantage of people’s natural curiosity or inclination to help. It can be as simple as handing your credit card to a waitress in a restaurant. The card is out of your sight, and they can scrawl down the number. It happens all the time.
It doesn’t matter how good your company’s firewall policy is if someone gets a phone call or if a human walks up to the front desk and begins asking questions or posing as someone they ought not to be. If you’re not educated on security, you want to help them.
JE: There aren’t enough cybersecurity experts to go around. What do we need to do to attract more people to the profession?
EB: In the US specifically, it’s not just cybersecurity, but there’s a dearth of STEM students entering colleges and universities. We have a youth culture that values the YouTube star and being famous for being famous. It’s not uncommon for some kids to think that there’s a quick way to success, and going to school for hard sciences, that seems too hard.
Another aspect is the American educational system. It needs to shift to a strong education and reward excellence. We’ve emphasized feelings, and I understand that it’s important to be considerate and thoughtful, but it’s come at the sacrifice of our educational system. You see it in the global rankings.
We need to move to strong education and promote hard sciences. It’s what drives the world forward. Doing hard things is how you get work done.
JE: There’s a lot of discussion about AI these days. Do you think AI will used for good or evil in cybersecurity?
EB: Yes. It will be used for good and evil.
I’m going to be skeptical here. My thoughts about AI, in whatever application but particularly in cybersecurity, is wake me up when we have something meaningful that applies.
We’re struggling with machine learning in networking. The data sets are getting better, but we don’t know what we don’t know and we’re not clear on what the algorithms are giving us back. Machine learning is the foundation for AI. Once we get machine learning, particularly with networking where you’re harvesting so much of the data that’s useful to cybersecurity, then AI will be built on that.
Going back to the good or evil question, there are potential use cases for good and certainly for bad, whether it’s privacy related, capitalist thinking or corporate greed. We’ll have both—right down to people who have no good intentions and use cybersecurity data and AI to figure out systems and work around them.
JE: Speaking of privacy concerns, do you have a smart home with devices that control the temperature or lighting?
EB: The Amazon lady—whom I dare not speak her name—is in my house. I primarily use Amazon Echo devices. My biggest use case is to control my Phillips Hue lights. I have a thing for lighting. I use the Amazon lady for playing music and occasionally to order something from the Empire of Jeff. It’s darn handy, even though I know she’s listening all the time.
JE:Who do you admire most in the security industry?
EB: Lately, it’s Johannes Ullrich, dean of research at the SANS Technology Institute. I listen to his SANS Internet Stormcast almost every day, and his insights into the latest cyber threats is invaluable. He’s a gifted communicator and accomplished security researcher, while at the same time coming across as someone you could have a good chat with over a beer.
JE: I have to ask: What's your current favorite meme?
EB: It’s from xkcd “How long you've had your smart appliance.”
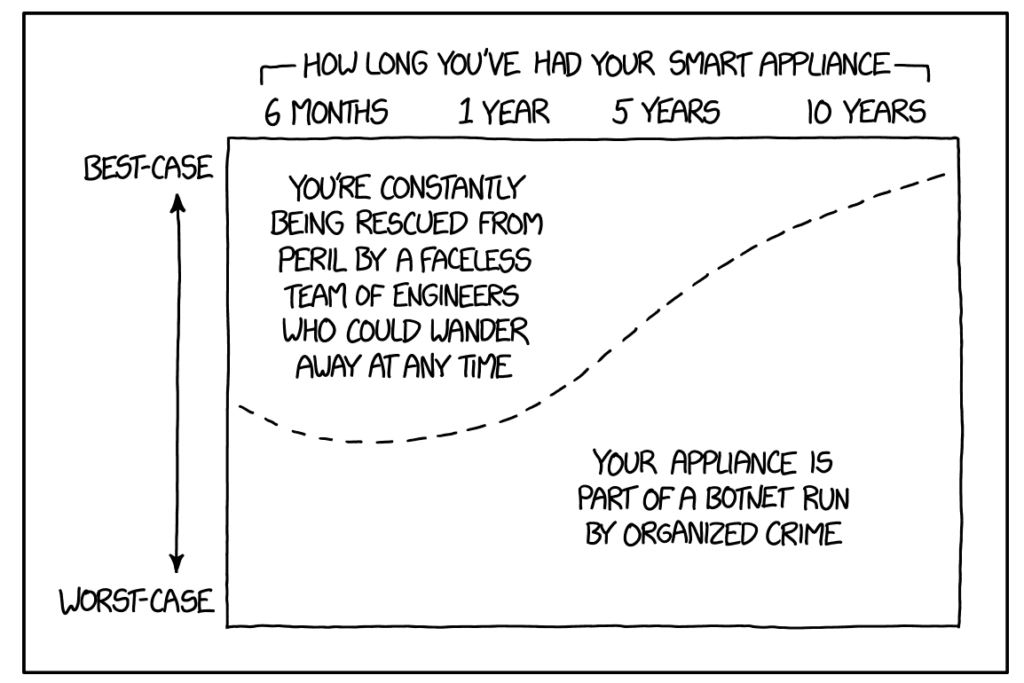
Source: https://imgs.xkcd.com/comics/smart_home_security.png
Ethan is a delegate at the Security Field Day on Fri., Dec. 14 at 9am PST.